- Cyber Safety
- Posts
- When Encryption Creates Overconfidence
When Encryption Creates Overconfidence
AI Agents Are Reading Your Docs. Are You Ready?
Last month, 48% of visitors to documentation sites across Mintlify were AI agents, not humans.
Claude Code, Cursor, and other coding agents are becoming the actual customers reading your docs. And they read everything.
This changes what good documentation means. Humans skim and forgive gaps. Agents methodically check every endpoint, read every guide, and compare you against alternatives with zero fatigue.
Your docs aren't just helping users anymore. They're your product's first interview with the machines deciding whether to recommend you.
That means: clear schema markup so agents can parse your content, real benchmarks instead of marketing fluff, open endpoints agents can actually test, and honest comparisons that emphasize strengths without hype.
Mintlify powers documentation for over 20,000 companies, reaching 100M+ people every year. We just raised a $45M Series B led by @a16z and @SalesforceVC to build the knowledge layer for the agent era.
Encrypted Doesn’t Mean Inaccessible
Data at rest may be encrypted, but once accessed by authorized users, it becomes readable. If credentials are compromised, encryption doesn’t stop misuse.
Key Management Is Often the Weakest Link
Encryption strength depends entirely on how keys are stored and rotated. Hardcoded keys or poorly secured key vaults undermine the entire system.
Endpoints Decrypt Everything
No matter how secure your storage is, user devices decrypt data for use. Compromised endpoints can capture sensitive information after decryption.
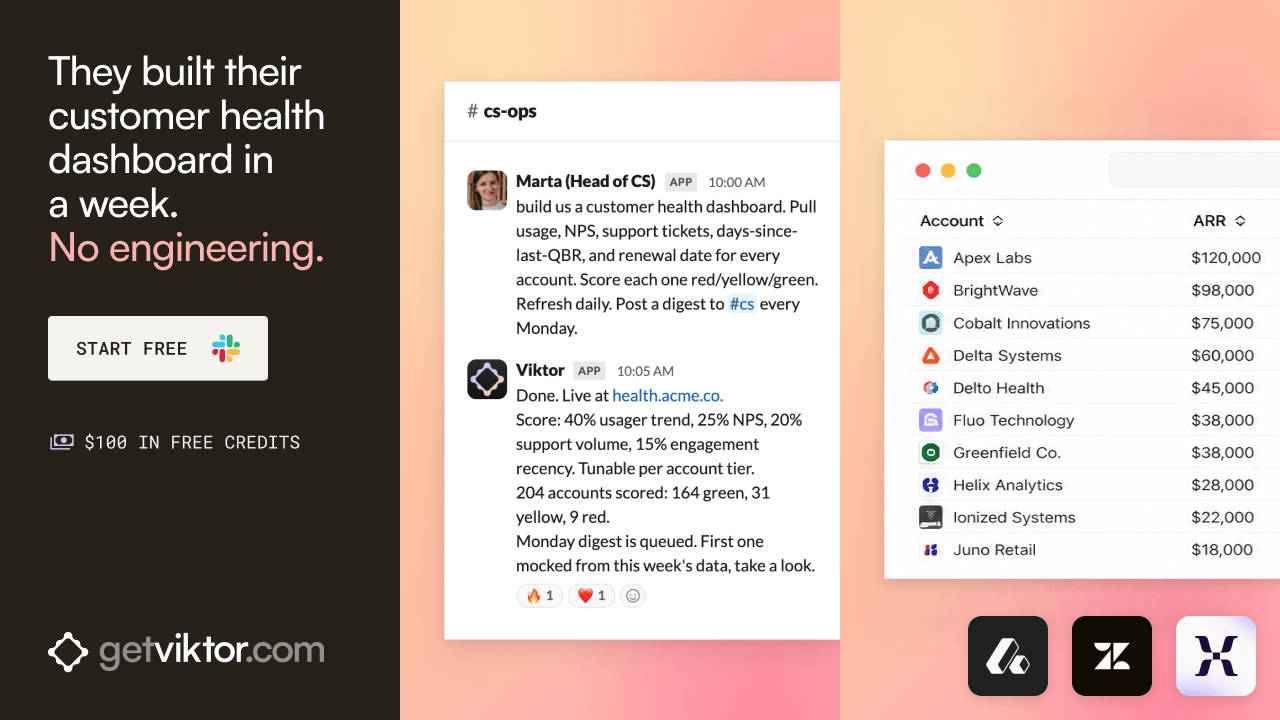
Your CS team stops waiting for engineering.
Every CS team has a wishlist. Health dashboard. QBR generator. Renewal command center. They sit in engineering's backlog for quarters.
A colleague in Slack ships the wishlist in a week. Hosted on your subdomain. Refreshes nightly.
84,000+ apps built on Viktor. SOC 2 certified. Your data never trains models.
Backup Encryption Is Frequently Overlooked
Production systems may be encrypted while backup archives are not. Attackers targeting backups can bypass frontline protections entirely.
Encryption Doesn’t Prevent Insider Abuse
Authorized users can still copy, export, or share encrypted data once decrypted. Monitoring and access control remain essential.
Encryption Is One Layer — Not the Strategy
Combine encryption with strong identity management, logging, segmentation, and anomaly detection. Protection must extend beyond the algorithm.
AI ads that look and feel like your brand
Most AI tools fall short because they lack context. They generate in a vacuum.
Hightouch Ad Studio uses your data and brand guidelines to produce high-quality creative. Refresh ads based on performance, react to trends, and respond to competitors instantly.
Less time prompting. More time launching.