- Cyber Safety
- Posts
- Trust Boundaries: Where Security Actually Breaks
Trust Boundaries: Where Security Actually Breaks
Same Kafka Protocol. Zero Kafka Baggage.
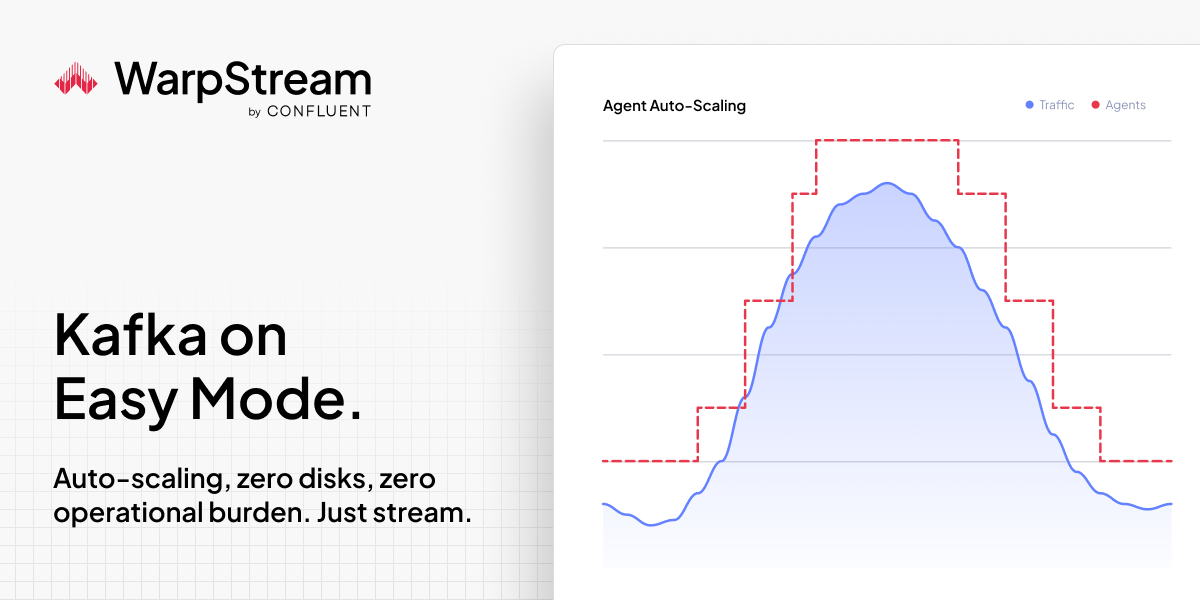
WarpStream BYOC speaks the Kafka protocol. Your existing clients, tools, and consumers work as-is. What disappears: local disks, partition rebalancing, inter-AZ fees, broker crashes, and capacity planning.
Agents auto-scale to match traffic automatically – no custom tooling, scripts, or operators required. Cursor's team reported spending zero hours thinking about scaling WarpStream. Character.AI called it operationally simpler at scale.
See how it works, then sign up free. Get $400 in credits that never expire. No credit card required to start.
Every System Has a Trust Boundary
Applications trust APIs. Employees trust emails. Networks trust internal traffic. Security failures often happen exactly where trust is assumed, not verified.
Internal Does Not Mean Safe
Many architectures still treat internal systems as trusted by default. Once an attacker breaches the perimeter, those assumptions collapse instantly.
Cross-System Integrations Blur Responsibility
When systems connect — CRM to finance, HR to payroll, cloud to on-prem — ownership becomes unclear. Gaps form at the intersection points.
Global HR shouldn't require five tools per country
Your company going global shouldn’t mean endless headaches. Deel’s free guide shows you how to unify payroll, onboarding, and compliance across every country you operate in. No more juggling separate systems for the US, Europe, and APAC. No more Slack messages filling gaps. Just one consolidated approach that scales.
Privilege Escalation Exploits Trust Chains
Attackers move through trust relationships: service accounts, federated identity, shared credentials. Each implicit trust becomes a stepping stone.
Unsanctioned tools create new trust zones outside security oversight. Data flows where controls do not.
Redefine Trust as Conditional
Zero Trust principles require constant verification across boundaries. Trust should be earned, time-limited, and continuously reassessed.
Gladly Connect Live '26. May 4–6 in Atlanta.
The room you want to be in. This is where CX leaders are tackling the hard AI questions and sharing what's actually working. For CX and ecommerce leaders. Atlanta, May 4–6. Space is limited — secure your spot now.