- Cyber Safety
- Posts
- The Myth of the Secure Perimeter
The Myth of the Secure Perimeter
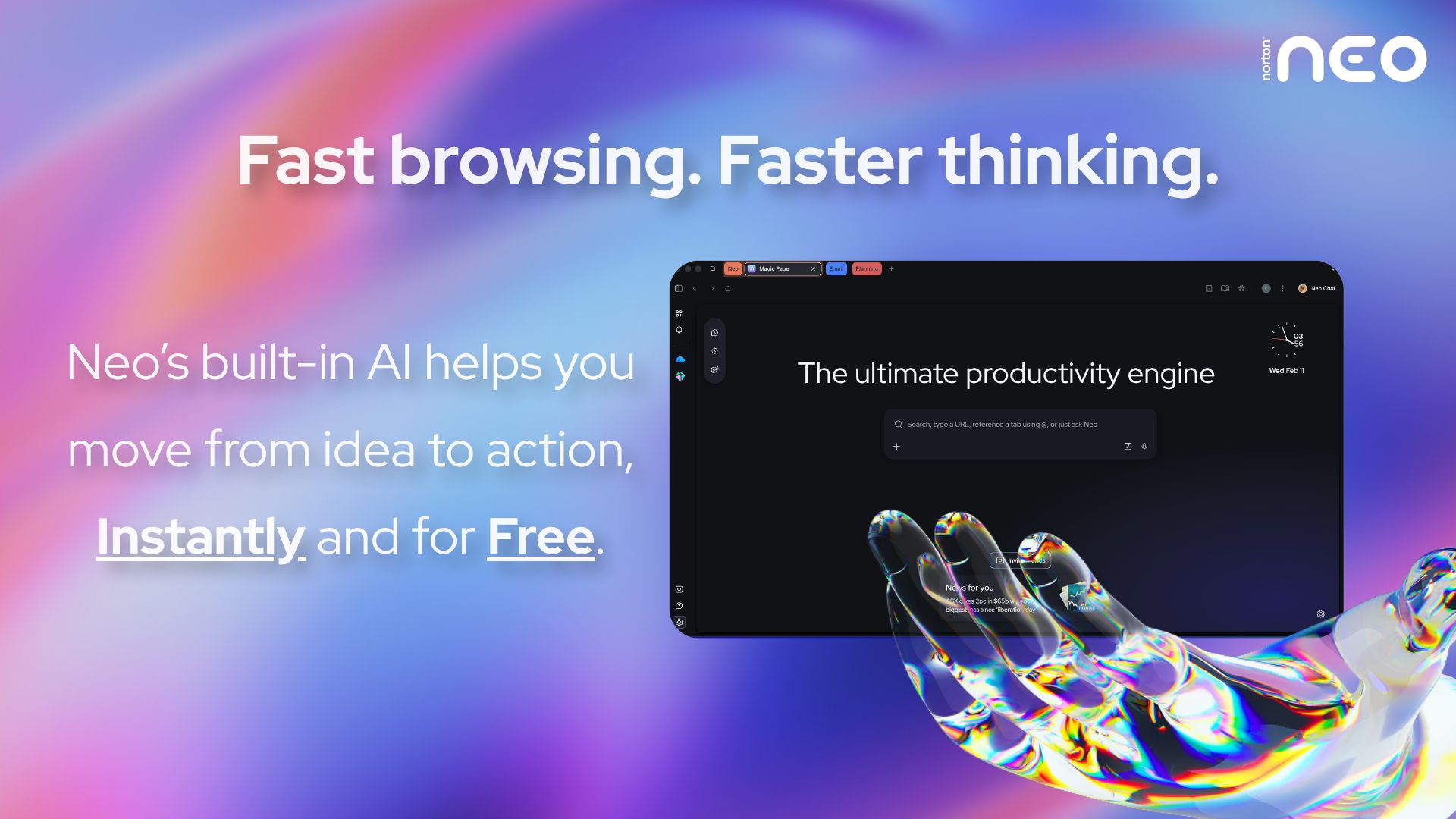
Fast browsing. Faster thinking.
Your browser gets you to a page. Norton Neo gets you to the answer. The first safe AI-native browser built by Norton moves with you from idea to action without slowing you down. Magic Box understands your intent before you finish typing. AI that works inside your flow, not beside it. No prompting. No copy-pasting. No switching apps.
Built-in AI, instantly and for free. Privacy handled by Norton. Built-in VPN and ad blocking protect you by default. No configuration. No extra apps. Nothing to think about.
Fast. Safe. Intelligent. That's Neo.
The Perimeter No Longer Exists
Cloud services, remote work, SaaS platforms, and mobile devices have dissolved the traditional network boundary. There is no single “inside” anymore.
Firewalls Don’t Stop Stolen Credentials
If an attacker logs in with valid credentials, perimeter defenses become irrelevant. Identity now matters more than location.
SaaS Lives Outside Your Network
Your CRM, HR tools, finance platforms, and collaboration apps operate beyond your firewall. Security must extend beyond on-prem infrastructure.
One editor for writers, developers, and agents
Most doc tools make you choose: accessible for writers, or git-native for developers. Mintlify's editor does both. Writers get WYSIWYG editing, developers keep their git workflow, and AI agents contribute via MCP. Every change syncs both ways. Your whole team, in one place.
VPNs Create a False Sense of Security
A VPN encrypts traffic — but once connected, users often gain broad internal access. Compromised accounts can exploit that trust instantly.
Modern Attacks Bypass Network Controls
Phishing, session hijacking, OAuth abuse — these attacks don’t care about your perimeter. They exploit identity and trust relationships.
Shift From Perimeter to Identity-Centric Security
Implement Zero Trust principles, continuous authentication, device posture checks, and strict access controls. The new perimeter is identity — and it must be verified constantly.
It's Monday. Every department already has context. Nobody prepped anything.
Your CFO opens Slack. There's a weekly Stripe revenue recap in #finance with a churned-accounts flag and a net-new breakdown. She didn't ask for it.
Your head of product opens Slack. There's a GitHub summary in private channel: PRs merged, PRs stale, Linear tickets that moved. He didn't ask for it.
Your marketing lead opens Slack. There's a Google Ads performance comparison in private channel, with a note: "Meta CPA crept up 18% this week. Might be worth pausing the broad match campaign." She didn't ask for it either.
All-hands at 10am. Everyone already knows the numbers. The meeting is about decisions, not catch-up.
That's what happens when one colleague works across every tool your company uses. Not one department's assistant. The whole company's coworker.
Viktor lives in Slack. Top 5 on Product Hunt, 130 comments. SOC 2 certified. Your data never trains models.
"Not only have we caught up on several months of work, we are automating manual tasks and expanding our operations to things previously not possible at scale." - Jesse Guarino, Director, Torque King 4x4